chapter
Tools Against Surveillance Capitalism
X VENDETTA
DO NOT SPEAK
We are living in an era where digital life is consolidated under billionaire owned platforms.
Owned by the few to govern the many. Our data is harvested and sold to oppressive regimes. The system profits from compliance and punishes deviation. Our conformity is rewarded. Our dissent is silenced. This is techno-fascism. And it’s not the only way.
De-Google Your Life
Google is not a search engine. It is a global behavioral intelligence contractor.
- Surveillance Capitalism: 80-85% of Google’s revenue comes from targeted advertising. Search, Gmail, Maps, Android = continuous tracking.
- Project Nimbus: Google & Amazon’s $1.2B cloud & Al contract with the Israeli government + military.
- Military Grade Al: Image recognition, data fusion, population surveillance. Used to target civilians in Palestine, the U.S. and worldwide.
- Algorithmic Censorship: Quiet de-ranking, demonetization, visibility control on topics that challenge the ruling ideology.
- Border Enforcement Ties: Cloud and data infrastructure complicity linked to immigration control and oppression by ICE.
- Environmental Extraction: Massive water, energy and resource requirements for AI compute.
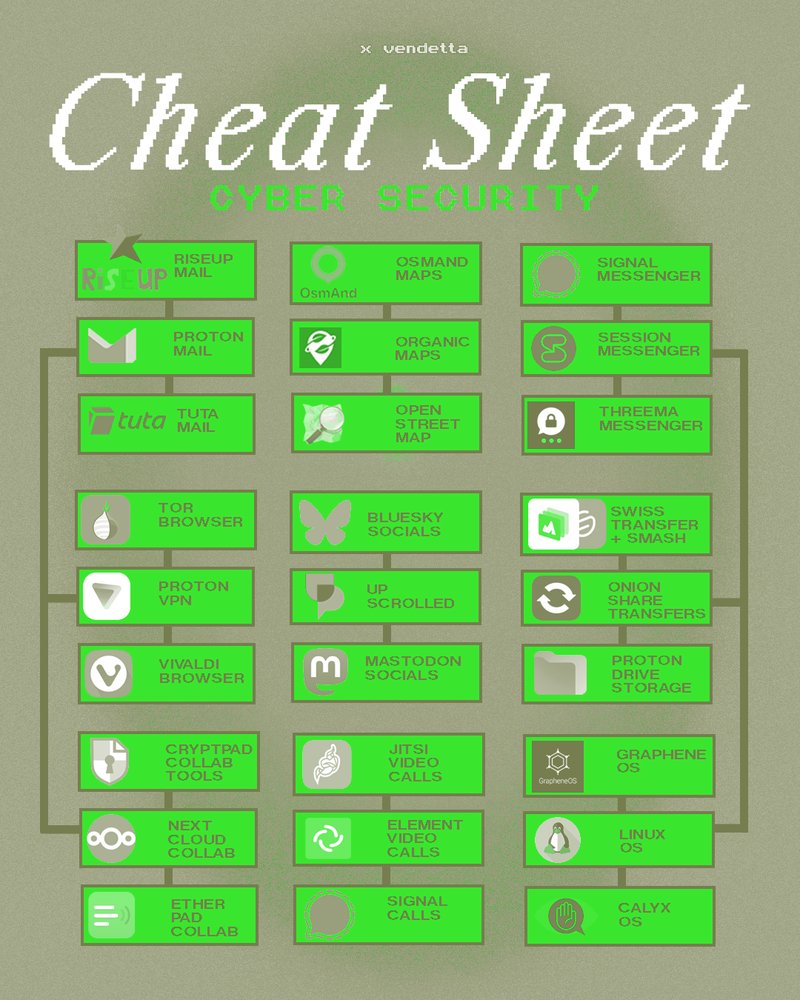
1. LEAVE: GMAIL / OUTLOOK
-
Microsoft tied to state and enterprise surveillance.
-
Gmail reads email content + scans attachments.
2. MOVE TO: END TO END ENCRYPTED, NON AD BASED MAIL
-
PROTON MAIL: Free encrypted mail server with calendar, VPN and other services. Proton cannot read your mail. Public key can be attached to your mail. Proton is a company so there are doubts on capitalization.
-
RISEUP MAIL: Volunteer-run anarchist data project. Offers secure, privacy-focused email and mailing list services. Requires an invite to join.
-
TUTA MAIL: Open source encrypted email service from Germany. Private company without outside investors. Removes IP from messages and uses AES and RSA encryption instead of PGP.
MAPS
1. LEAVE: GOOGLE MAPS
-
Maps = location history, movement patterns, daily routines.
-
Google maps centralizes global mobility data.
2. CHOOSE: OPEN DATA OR FEDERATED ALTERNATIVES
-
OPEN STREET MAP: Community-built, open-source world map. No single owner; data created and maintained by volunteers globally. Anyone can audit, host, or reuse the data.
-
ORGANIC MAPS: Offline-first mobile maps built on OpenStreetMap. No trackers, no ads, no data collection. Works without internet once downloaded.
-
OSMAND MAPS: Highly customizable navigation app using OpenStreetMapdata. Supports offline use, local data storage, and user control over what is shared.
MESSAGING
1. LEAVE: WHATSAPP / FB MESSENGER
-
Easiest ways to infiltrate movements.
-
Avoid meta owned platforms.
2. PRIORITIZE: E2EE + MINIMAL METADATA
-
SIGNAL: Fully open-source, commonly used, based in USA. End-to-end encrypted messaging with minimal metadata. Widely audited - requires phone number.
-
THREEMA: Paid, privacy first messaging app with strong encryption and no data harvesting. Not open source, no self-destruct.
-
SESSION: Decentralized, onion routed messaging that does not require a phone number. Designed for anonymity.
BROWSING
1. LEAVE: CHROME / SAFARI
-
Assume you are being watched. Browsers fingerprint you by default.
-
Isp’s log traffic. States subpoena it. We are exposed to tracking.
2. PRIORITIZE: ANONYMITY + ENCRYPTION
-
TOR BROWSER: Free overlay network for enabling anonymous communication. Built on free, open-source software run by volunteer-operated relays worldwide. Brave browser has one integrated.
-
VIVALDI BROWSER: Built-in ad & tracker blocker. Highly customizable. High privacy and user community. Alternative to Brave browser after concerns of CEO homophobia and big-tech ties. Non open-source.
-
PROTON VPN: Virtual private network change user’s device IP to another location to bypass location-based restrictions and block trackers. Proton is Swiss-based with high data protection laws.
SOCIALS
1. META / X / TIKTOK ARE COOPTED BY ZIO CORPS & BILLIONAIRES
-
Corporate platforms silence and censor dissent.
-
Engagement algorithms = behaviour & belief shaping.
2. CHOOSE: DECENTRALIZED & USER OWNED NETWORKS
-
UPSCROLLED: Palestinian owned, fair algorithms, no shadow-banning, company owned, never biased, social responsibility, more transparency.
-
MASTODON SOCIALS: Part of federated (decentralized) social media network. Open-source, not for sale, interoperable. Allows for photos, videos and microblogging.
TRANSFER / STORAGE
1. LEAVE, AVOID: GOOGLE DRIVE / DROPBOX / ONEDRIVE / ICLOUD / AWS POWERED APPS
-
Files scanned, indexed, retained on centralized servers. Not e2e by default. Can access your files + data.
-
Enterprise + state-aligned infrastructure. Subject to law enforcement access.
2. PRIORITIZE: ENCRYPTION + AUTO-DELETION BY DEFAULT
-
PROTON DRIVE: End-to-end encrypted storage. Provider cannot read your files. Expiring links + user-controlled access. Cloud without surveillance.
-
ONION SHARE: Peer-to-peer file sharing over Tor. No central server, no logs, no permanent storage. Maximum de-centralization.
-
SWISS TRANSFER: Software for free file transfer up to 50GB, files stored in Switzerland, files available 30 days before destroyed, password protection possible.
-
SMASH: Unlimited file size transfer possible, no advertisement, customizable links possible, password protection and file previews possible.
COLLAB TOOLS
1. LEAVE, AVOID: GOOGLE DOCS / OFFICE 365 / NOTION
-
Centralized, enterprise-first infrastructure, no e2e and long data retention.
-
Documents scanned, indexed and retained on Google servers.
2. CHOOSE: PRIVACY-FIRST, SELF-HOSTABLE TOOLS
-
CYPT PAD: Collaborative office suite. End-to-end encrypted. Open-source. Includes docs, forms, spreadsheets and many more. Allows for password protection. True private collaboration, not just storage.
-
NEXT CLOUD: Self-hostable collaboration suite (files, docs, chat). You choose where data lives and who controls it. Collaboration without corporate ownership.
-
ETHERPAD: Lightweight, open-source, real-time text editing. can be self-hosted, no accounts required. Fast, disposable collaboration with minimal data exhaust.
VIDEO CALLS
1. LEAVE, AVOID: GOOGLE MEETS / ZOOM / TEAMS / FACETIME / BOTIM, COMERA
-
Centralized, enterprise-first infrastructure, no e2e and long data retention.
-
Documents scanned, indexed and retained on Google servers.
2. CHOOSE: PRIVACY-FIRST, SELF-HOSTABLE TOOLS
-
JITSI: Encrypted, open-source free software. A one-time custom link can be created within seconds. Allows easy screen sharing and anonymous participation.
-
ELEMENT (MATRIX): Encrypted calls built on a federated protocol. Users can self-host servers and control data. Communication without platform lock-in.
-
SIGNAL CALLS: End-to-end encrypted voice and video. Minimal metadata, no meeting logs or cloud recordings. Conversations stay ephemeral.
OPERATING SYSTEMS
1. BEWARE OF: WINDOWS / MAC OS / ANDROID / IOS
-
OS level surveillance = total visibility. Cloud dependency is baked into core functions.
-
Android & ios track & monetize behavioural data. iCloud ties system behaviour to centralized servers.
2. CHOOSE: OPEN-SOURCE & DE-GOOGLED SYSTEMS
-
LNUX OS (UBUNTU, FEDORA): Safer & faster than Windows since many apps are not automatically pre-installed and virus writers tend to go for lower-hanging fruit. Open source and free with alternative to MS office called Libre.
-
GRAPHENE OS: Private and secure, developed as a non-profit open source project. Currently only works on Google Pixel 6 and above. Is the only mobile OS which Israeli decryption software Pegasus cannot crack.
-
CALYX OS: Privacy-focused Android alternative. Removes Google tracking while keeping usability.